Exe0.1 Winnie Soon
At the time of execution: throbber.start()
Loading images and webpages, waiting for social media feeds and streaming videos have become a massively cultural activity involving the complexity of real-time data processing. In many situations, users encounter a notable and animated spinning icon, a logo calls throbber, which tells the user something is work-in-progress, but nothing more. Unlike a progress bar, a throbber is repeatedly spinning under a constant speed. In contrast to a progress bar, a throbber does not indicate the percentage of a completed and unfinished process. Sometimes text will be given in conjunction with a progress bar, explaining the processual tasks, for example, transferring and copying files, and installation procedures. This explanation is commonly seen in software installation, and/or something that are related to computer operations. Arguably, when a program is connected to a technological network, in particular a home or a mobile network that requires the Internet protocol of TCP/IP, things are getting more complex, and hence less predictable.
This short article focuses at the time of execution, especially the time when data buffering occurs. It investigates the temporal complexity of real-time data processing, in which code inter-actions [1] are constantly occurs. The representation of data, in the forms of images, webpages, feeds and videos, is generated by the process of code that inter-acts with protocols, databases, memory, machines and amongst others. Data buffering is what Karen Barad might describe as “things-in-phenomena”(2007, p. 140). Such phenomena with no individual constituted agents or pre-existing entities, but rather needs to be understood as entanglement. In view of the fact that data buffering becomes part of our everyday culture and daily encounter, but the process is seemingly hidden behind, and yet entangled with a cultural throbber icon.
Following the tradition of ‘Software Studies’, this article is informed by a close reading of an entangled throbber and cold gazing [2] of the operational logics of data buffering. It draws upon the concept of “microtemporality” in the work of Wolfgang Ernst (2013), as well as his time-critical perspective on the notion of “discontinuity” (2006) which is based on Michel Foucault’s famous work, entitled The Archaeology of Knowledge. According to Foucault, his notion of discontinuity offers an alternative perspective in understanding knowledge beyond its stable form of narration and representation (1972, p. 3). Both Foucault and Ernst use the term discontinuity by means of examining the gaps, silence and ruptures of things that go beyond representation. Although a throbber icon becomes a standard way of implementation in contemporary software culture, each network and connection reacts differently with its own microtemporality. The conception of time should be moved beyond a user-centric understanding of time perception, such as waiting time, loading time and streaming time, but to understand time that are entangled with code inter-actions. The appearance of a throbber icon executes not only the disruption of data representation, but also the unpredictability of network entanglement that are specifically experienced in contemporary software culture.
A cultural reading of a throbber
A throbber icon is increasingly exposed to our everyday life, it acts as an interface between computational processes and visual communication. With its distinct characteristic of spinning design that indicates background processing, one of the earliest use of a throbber can be found in the menu bar of a Mosaic web browser in the early 1990s, developed by National Center for Supercomputing Applications (NCSA) (Albers, 1996; Roebuck, 2011) and the browser interface was designed by scientist Colleen Bushell. The throbber contains a letter ’S’ and a globe that could spin when loading a web page. This kind of a spinning throbber, with the company browser’s graphical logo, has been also seen in subsequent software browsers. While a throbber spins, it visually indicates actions are in progress. These actions, from a user point of view, could be interpreted as the loading of web data or connecting to a website by a software browser. From a technical perspective, it involves data transmission across Internet, as well as a browser that renders the inter-actions of code. The spinning behavior is stopped when a webpage is loaded within a browser. A web browser, according to Tali Garsiel and Paul Irish (2011), is a software able to render and display requested content, make network calls and requests, and store data locally. In this respect, the spinning throbber icon represents a complex inter-actions of code under a network. A throbber with its spinning characteristic, therefore, can be said is rooted in, and is specific to, the Internet culture.
In more recently, a throbber icon does not only attach within a software browser, it also appears in different web and mobile applications, social media platforms in particular. A throbber transforms into a spinning wheel that consists of lines or circles that are arranged in radial and circular form, moving in a clockwise direction. Each individual element of a wheel sequentially fades in and out constantly and repeatedly that creates a sense of animated motion (see Figure 1). These types of spinning wheel appear after one has triggered by an action, such as swiping a screen with feeds in order to request for most updated information to appear on a screen. It also appears after one has confirmed an online payment, waiting for a transaction to complete. Most obviously, it is seen when one cannot watch a video clip smoothly over the Internet. As a result, an animated throbber appears as a spinning wheel on a black color background, occupying the whole video screen while video buffering is encountered.
Figure 1: Throbber sequences in the form of circles and lines. Image is retrieved from http://designmodo.com/css3-jquery-loading-animations.
Emotionally, it is annoying and frustrating while one encounters buffering because it involves interruption (Broida, , n.d; Stelter, 2011). Things do not flow smoothly and users become less patient to wait for an unknown time period. Contemporary artists, such as Gordan Savičić [3], have explored this challenge of time perception. Perhaps, there is an expectation of things that flows continuously like in Television programs. The notion of flow is famously theorized by a media scholar Raymond William in 1974, in which the programming of content implies continuity that is based on the experience of viewing and reception (1974, pp. 80-84). The interruption, what William calls “natural break”, of the advertisement in Television, is a planned flow as part of the TV production (Williams, 1974, p. 90). Most importantly, the notion of flow is a planned sequence (Williams, 1974, p. 93), and therefore exhibits a relatively stable temporality. However in the digital medium like an Internet network, the interruption, such as buffering, cannot be planned as it is subjected to the technical conditioning at the moment of time. This notion of discontinuity might not be visible to users/viewers due to a short interruption time (less than 1 second [4]), but what is needed here is to understand the material nature of discontinuity in networked medium as part of the computational culture, which exhibits something I refer as discontinuous temporality.
Discontinuity in networked medium
The network structure of today’s communication channels and of their information stream is often understood as providing a direct connection between users and services or between two communication partners, even though there cannot be any direct connections on digital networks. The metaphor of the flow conceals the fact that, technically, what is taking place is quite the opposite. There is no stream in digital networks. (Sprenger, 2015, pp. 88-89, my emphasis)
The notion of temporality is understood here as differences and rhythms. In a general sense, data is generated in different circumstances in the network environment - in relation to different speeds and spaces. In the context of data buffering within computational networks, temporality refers to the processing and the unfolding of data over time that generates differences and rhythms. The term data buffering does not limit to videos, images or text as a representation, rather it focuses on the material infrastructure and operational computational logics underneath a representational screen. Although there are numerous scholarly works discuss temporality in relation to the subjectivity of time (Berry et al., 2012, p. 57), I am more interested in the material aspect and the nondiscursive realm of temporality. It is similar to how Wolfgang Ernst describes as microtemporality, focusing on the micro-temporal processes, that are related to the nature of signals and communications, mathematics and digital computation within its deep internal and operational structure (2013, pp. 186-189). In other words, microtemporality is about examining and understanding technical conditionings that are beyond human perception.
In today’s networked communication, data is constantly perceived as stream (Berry, 2011, 2012, 2013; Chatzichristodoulou, 2012; Fuller, 2003) with its vast volume, speedy update and delivery. However, Florian Sprenger reminds us that the notion of flow and stream are metaphors (2015, pp. 88-89). The temporality of the perceived flow/stream involves unperceivable discrete-time system (Ernst, 2006, p. 108), data packets transmission (Baran, 2002; Sprenger, 2015, pp. 73-102), temporal storage and transfer (Ernst, 2006, p. 108; Haykin & Moher, 2007, p. 8) and micro-decisions by protocols (Sprenger, 2015). All these made the network should be regarded as discontinuous, rather than continuous. Indeed, all these produce differences and rhythms due to the fact that computation is about calculations, mathematics and logics that are executing and running in real time. The implication is that these operative processing cannot be seen as a planned sequence or flow, there is a live dimension of such operative logics that reconfigure the understanding of time and temporality in computational process.
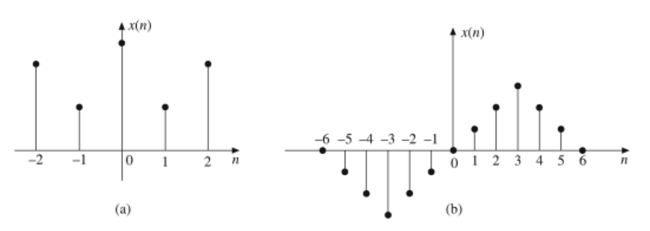
As opposed to continuous-time signals in analogue system, digital adopts the model of discrete-time system with independent variables, where input and output are regarded as discrete-time signals. This means that each discrete state is countable and measurable with a distinct value, and can be represented by a sequence of numbers (Kumar, 2015, pp. 3-5). The signals are discrete in time (see Figure 2), which means there is no value between time intervals (Kumar, 2015, p. 17). The ‘flow’ of data that we experience through data representation is, therefore, regarded as a discrete moment in time.
In the early design of modern communication network, the concept of packet switching is fundamental to understand how data flows in a technological network. Data streams are chopped into smaller blocks as packets that send over a communication channel in and through different routes, rates and sequences, which is known as packet switching (Baran, 2002). According to Paul Baran, one of the inventors of packet switched computer network, real-time connection between sender (transmitting end) and user (receiving end) is an illusion. It is because the fast enough data rate that able to give a sense of real-time connection (Baran, 2002, pp. 43-4). Importantly, the routing of a packet data has to transmit through different nodes and routers. Although a selected path is based on “adaptive learning of past traffic”, there are real-time decisions that have to be made to locate a shortest path due to the dynamic of network conditions (Baran, 2002, p. 44). In other words, data travels “via highly circuitous paths that could not be determined in advance” (Baran, 2002, p. 43). Since data packets are inscribed with serial number and the function of checksum that made them possible to reformulate a correct sequence that can be perceived as representation, this assembling process involves temporary buffer. Baran explains as follow:
On the transmitting end, the functions include chopping the data stream into packets, adding housekeeping information and end-to-end error control information to the out-going packets. On the receiving end, each multiplexing station uses terminating buffers temporarily assigned to each end addressee to unscramble the order of the arrived packets, and buffer them so that they come out as an error-free stream, only slightly but not noticeably delayed. (Baran, 2002, p. 46)
What is important here is the merely noticeable delay time, as well as the availability of temporarily storage area as buffer for data assembling, which give the perception and illusion of stream. In such a journey of data packet transmission, Sprenger argues there are numerous “micro-decisions” that are made through network protocols, such as the decision of locating “the most efficient path to the destination”, the speed of data processing and “the priority of incoming packets” (2015, p. 19). All these decisions are made to control how data is distributed, even sometimes the required decision or the algorithmic time is not significant, but still there is time lost along the journey (Sprenger, 2015, p. 75). This journey includes different nodes, transmitting and receiving ends in which data disassembling and assembling occur. As such, “[t]he stream never flows uninterruptedly” (2015, p. 19). This constant interrupting microtemporality includes decision-making processes, controls and regulations that are programmed at the level of code and are inscribed in the computational and calculational processes. When micro-decisions take account of law and rules in network environments, data does not unfold continuously, rather as what Derrida points to the “continuous unfolding of a calculable process” (2002, p. 252).
Figure 2: Discrete time signals. Reprinted from Digital Signal Processing (p. 18), by A. A. Kumar, Year, Delhi: PHI Learning Private Limited. Copyright 2015 by PHI Learning Private Limited.
Calculable processes do not only occur at the network level, but also at the memory and storage level which is highly relevant to code execution. In computer science, buffer is a memory area for “temporary data storage”, involving both hardware and software level (Laplante, 2000, p. 55). An example would be loading an image from a webpage, data is received at the receiver’s end (as input data) and is stored temporary until the data is further processed by software application (as output data). In this image example, the buffer memory is where a browser accesses the input data and retrieves it as output data; subsequently, a browser displays the data as an image gradually [5] loads on a screen. Buffer refers not only image or video data, but all kinds of data with different “data transfer rates and/or data processing rates between sender and receiver” (Laplante, 2000, p. 55). Furthermore, Ernst reminds the processing of data consists not only the transferring part, but “a coupling of storage and transfer in realtime”, he explains, “While we see one part of the video on screen, the next part is already loaded in the background” (2006, p. 108). The process of such input and output of data is called buffering. This process involves not only temporary storage, but also transfer in different rates and time. Indeed, the purpose of buffering is highly related to time, as the main purpose of a buffer “is to reduce time dependencies of the data and to decouple input/output from the program execution”. As a result, data can be consumed (as input) and processed (as output) at a different rate (Laplante, 2000, p. 55). Therefore, the execution of code, in this network environment, exhibits the microtemporality of data processing.
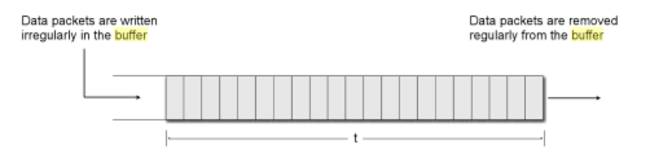
Theoretically, Just in Time (JIT) delivery is used in streaming media to prevent noticeable buffering. The relatively big size of data, such as audio or video, is transmitted as numerous segments at one of the architectural network layers (usually via RTP protocol), but a media player does not require to wait for the entire media file to be downloaded. JIT allows to playback the partial received data that is just enough to temporary store at the client’s buffer (Pereira & Ebrahimi, 2002, p. 260). In this sense, both playbacks the buffer data and receiving the remaining data can be made simultaneously. Ideally, according to Meinel and Sack, “the playback buffer empties itself at one end just as quickly as it fills up at the other end”. If there is transmission delay that is within a threshold time t, it is regarded as unnoticeable in playback (2013, p. 783). On the contrary, a throbber icon will be appeared when there is a delay of individual data segment that exceeds the threshold time t. It is commonly seen in social media sites, such as Youku or Youtube, whereby this situation is mostly due to the instability or low bandwidth of a network that causes the delay of data segment arrival. Regardless of the exceeding or within the threshold time t, streaming “is achieved by buffering the transmitted data before the actual display” (Meinel & Sack, 2013, p. 780). The buffer, in the case of playback buffer, is actively and constantly being stored (write) and removed (read) in different rhythms (see Figure 3), oscillating between the invisible and visible, and this is how we can only immanently experience such microtemporality.
Figure 3: Principle organization of a playback buffer. Reprinted from Internetworking: Technological Foundations and Applications (p. 783), by Christoph Meinel & Harald Sack, 2013, Berlin: Springer. Copyright 2013 by Springer.
From the operative logic of streaming, we know there is a continuous data processing, reading and writing of buffer in particular. The operative logic is automated, and is built within the infrastructure of software as code. However, the automated algorithm only can read what has been written in the buffer. It does not guarantee if all the data are written in the buffer. Dropped frames is a relatively common experience in real-time communication or video streaming, it refers to frames of video that are dropped during playout. Technically, such data loss is mostly caused by network congestion, resulting in the absence of certain parts of data that calls packet loss (Kurose & Ross, 2013, p. 327). Packet loss does not only limit to streaming applications, but such lost frames/data are more apparent in real-time conversational applications, such as Skype, and media streaming platforms, such as Youtube. Data loss is related to the degradation of quality, and it could immediately impact the visual or audio quality, hence jitters or glitches could be experienced directly by an end user. A serious data loss may even result in the termination of a connection automatically. Indeed, the consequence of data loss is not so much of my concern here, but the potentiality of data drops and its implications are somewhat rather with significance. Data packets are not only transmitted at different rates (speed), but also with the potential to be dropped at any time. In addition, those dropped packets might not cause noticeable effects in digital communication as it is subjected to the amount of loss. As such, those dropped packets might be insignificant in the entire user experience, which also means they are relatively silence. As long as a network connection is still maintained, the silence and the absence of data packets reconfigure the temporality of networks through its automated micro-decisions and processes. As I explain earlier, the silence of data dropped is not necessarily a noticeable interruption in terms of both user and network level. On the one hand, it can be seamless to user’s perception; on the other, those lost packets are just being automatically ignored as part of the data processing logics. Therefore, there are micro-things that are not only invisible and silence, but also absence as well. The microtemporality of network requires to understand the potential and the actual absence and silence of dropped frames and packets loss.
The microtemporality of code inter-actions, including data, code and technological network, is something that I refer to discontinuous temporality. In this contemporary software culture, things are immanently networked and data are constantly generated. The notion of execution perhaps require to understand beyond mere code instructions, and to include the perspective of code inter-actions. Such discontinuous temporality highlights not only the differences and rhythms of code execution, and its inter-actions with data and network, but also the absence and silence of data that go beyond the representation. The complex process of data buffering, as I argue, exhibit a very particular kind of discontinuous temporality that sheds light on the real-time dynamics of computational networks. With both the fragility of networks and automated data processing, the things that processed on screen, as I argue, is never in a full and in a completed picture. Therefore, the temporal and fragmented representations imply discrete blocks of (social) unreality. The computational processing and reprocessing, such as storing, transferring and buffering, of network communication exhibit very particular forms of discontinuous temporality that can be only immanently experienced.
>>>>> end here basically. But actually there are so many things can elaborate on such as no recovery of packet loss in UDP protocol, micro-decisions in relation to reliability and speed, re-sending and reproduction of lost packet and more on the implications. I just don't have the space to expand here.
Notes
[1]The notion of inter-actions as a framework is something that I am developing with my PhD thesis. It mainly draws references from the notion of "interaction" (Wegner, 1997; Bentley, 2003) from Computer Science and the notion of "intra-actions" (Barad, 2007) from Philosophy. Code inter-actions highlight the operational process of things happen within and across machines through different technical substrates. In addition, phenomena is produced through machine behaviors that are changing at different and multiple levels and scales that is understood as entanglement. The concept of entanglement is associated with agency, it is constantly "inter-acting from within, and as part of, the phenomena produced" (Barad, 2007, p. 36)
[2]Cold gazing is a method proposed by Wolfgang Ernst in the field of Media Archaeology. It is used to engage with the mechanical and operational logic of computation (Parikka, 2011, 2012). This method of cold gaze describes cold facts, but not stories or interpretation, which is distinctly object-oriented, nonhuman-focused, and not narrative-based (Parikka, 2012, pp. 8-9).
[3]See the artistic project Loading by Gordan Savičić http://www.yugo.at/processing/index.php?what=loadinghttp://www.yugo.at/processing/index.php?what=loading [Thanks for Eric Enodgrass who points me to Gordan's work]; Other artists also explored the design of a Throbber icon, see Fedora Artwork team’s throbber work: https://fedoraproject.org/wiki/Artwork/ArtTeamProjects/Fedora7Remix/Rhgb/Throbber
[4]In mobile networks, such as GPRS, the data rate can be up to 21.4 kb/s. See more here: Ferng, H.W & Tsai, Y.C. (2005) Using Priority, Buffering, Threshold Control, and Reservation Techniques to Improve Channel-Allocation Schemes. IEEE Transactions on Vehicular Technology. 54 (1).
[5]An image, in general, can be displayed in the form of interlace or progressive format. See here: Greenspan 2003. Adding Images to Your Site- http://philip.greenspun.com/panda/images
References
- Albers, M. C. (1996). Auditory cues for browsing, surfing, and navigating. Proceedings of the 3rd International Conference on Auditory Display (ICAD 1996), Palo Alto, California. Retrieved from https://smartech.gatech.edu/handle/1853/50793
- Barad, K. (2007). Meeting the universe halfway : quantum physics and the entanglement of matter and meaning (Reprint. ed.). Durham: Duke University Press.
- Baran, P. (2002). The beginnings of packet switching: Some underlying concepts. IEEE Communications Magazine, 40(7), 42-48. doi:10.1109/MCOM.2002.1018006
- Berry, D. M. (2011). The philosophy of software Code and mediation in the digital age. Basingstoke: Palgrave Macmillan.
- Berry, D. M. (2012). The Social Epistemologies of Software. Social Epistemology, 26(3-4), 379-398. doi:10.1080/02691728.2012.727191
- Berry, D. M. (2013). Introduction: What is code and software? Life in Code and Software: Mediated Life in a Complex Computational Ecology: Open Humanities Press.
- Berry, D. M., Dartel, M. v., Dieter, M., Kasprzak, M., Muller, N., O'Reilly, R., & Vicente, J. L. d. (2012). New Aesthetic, New Anxieties: V2_Institute for Unstable Media.
- Broida, R. Stop Frustrating Pauses in YouTube Videos. http://www.pcworld.com/article/201089/Stop_Frustrating_Pauses_in_YouTube_Videos.html Retrieved from http://www.pcworld.com/article/201089/Stop_Frustrating_Pauses_in_YouTube_Videos.html
- Chatzichristodoulou, M. (2012). Cyberformance? Digital or Networked Performance? Cybertheaters? Or Virtual Theatres? … or all of the above? Paper presented at the Cyposium: cyberformance symposium. http://www.cyposium.net/selected-presentations/chatzichristodoulou/
- Derrida, J. (2002). Acts of religion. New York: Routledge.
- Ernst, W. (2006). Dis/continuities: Does the Archive Become Metaphorical in Multi-Media Space? In W. H. K. Chun & T. Keenan (Eds.), New media, old media : a history and theory reader (pp. x, 418 sider). New York ; London: Routledge.
- Ernst, W. (2013). Digital Memeory and the Archive. Minneapolis: University of Minnesota Press.
- Foucault, M. (1972). The archaeology of knowledge and the Discourse on language. New York: Pantheon Books.
- Fuller, M. (2003). Behind the blip : essays on the culture of software. New York
London: Autonomedia;Pluto.
- Garsiel, T., & Irish, P. (2011). How Browsers Work: Behind the scenes of modern web browsers. Retrieved from How Browsers Work website: http://www.html5rocks.com/en/tutorials/internals/howbrowserswork/ Retrieved from http://www.html5rocks.com/en/tutorials/internals/howbrowserswork/
- Haykin, S., & Moher, M. (2007). Introduction to analog and digital communications (2nd ed.). Hoboken, N.J.: Wiley.
- Kumar, A. A. (2015). Digital Signal Processing, Second Edition. Delhi: PHI Learning Private Limited.
- Kurose, J. F., & Ross, K. W. (2013). Computer Networking: A Top-Down Approach: Pearson Education.
- Laplante, P. A. (2000). Dictionary of Computer Science, Engineering and Technology CRC Press.
- Meinel, C., & Sack, H. (2013). Internetworking: Technological Foundations and Applications. Berlin: Springer.
- Parikka, J. (2011). Operative Media Archaeology: Wolfgang Ernst's Materialist Media Diagrammatics. Theory, Culture & Society, 28(5), 52-74.
- Parikka, J. (2012). Archival Media Theory: An introduction to Wolfgang Ernst's Media Archaeology Digital Memory and the Archive. Minneapolis: University of Minnesota Press
- Pereira, F., & Ebrahimi, T. (2002). The MPEG-4 Book: Prentice Hall.
- Roebuck, K. (2011). Virtual Desktops : High-impact Strategies - What You Need to Know: Definitions, Adoptions, Impact, Benefits, Maturity, Vendors. Dayboro: Emereo Publishing.
- Sprenger, F. (2015). The Politics of Micro-Decisions: Edward Snowden, Net Neutrality, and the Architectures of the Internet: meson press, Hybrid Publishing Lab, Centre for Digital Cultures, Leuphana University of Lüneburg.
- Stelter, B. (2011). Debate Web Stream Does Not Flow Smoothly for All. Retrieved from http://thecaucus.blogs.nytimes.com/2011/10/11/debate-web-stream-does-not-flow-smoothly-for-all/?_r=1
- Williams, R. (1974). Television : technology and cultural form. London: Fontana, Collins.